Researchers show how malicious apps can control Samsung SmartThings locks, lights and more [Video]
![Researchers show how malicious apps can control Samsung SmartThings locks, lights and more [Video]](https://cdn.runwayritz.com/2026/02/Researchers-show-how-malicious-apps-can-control-Samsung-SmartThings-locks-780x470.png)
Update: Samsung released a statement to us, which recently expanded on its previous response. You can read it below the video.
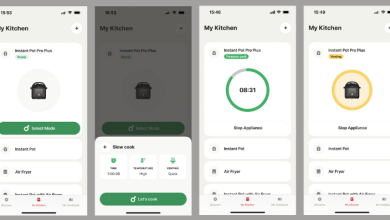
Computer science researchers from the University of Michigan have demonstrated how malicious apps can control Internet of Things devices on Samsung’s SmartThings platform – including the ability for an attacker to open the front door to gain physical access to the home.
The main weakness identified is that the SmartThings platform grants applications more privileges than are necessary to perform their specified functions, reports The Verge.
The researchers demonstrated these findings with a proof-of-concept app that promises to monitor battery life on a variety of devices. If the user agreed to allow a malicious – but seemingly innocent – application to access their smart key, the researchers could not only monitor its battery, but also perform other functions of the lock, including opening the door. Researchers found 42 percent of the 499 analyzed SmartApps are currently overprivileged in the same way…
A second exploit allowed the team to program their own PIN codes on the door to allow physical access at will.
Although the user will need to install the malicious application, a small user survey showed that it is not difficult to persuade non-technical users to do so.
Ninety-one percent said they would allow a battery monitoring app to check their smart lock, and therefore give the app access to its functions.
Samsung says it’s issuing updated guidelines to developers on securing their code, and that it’s conducting app updates. The Michigan team now, however, believes this will be enough.
The risks are significant, and likely won’t be easily solved with simple security patches.
You can watch a video demo below.
Protecting our customers’ privacy and data security is central to everything we do at SmartThings. We regularly perform penetration testing of our system and communicate with third-party security experts, accepting their research to stay ahead of any potential threats and be industry leaders when it comes to our platform’s security.
We are fully aware of the University of Michigan/Microsoft Research report and have been working with the report’s authors for the past several weeks on ways to continue making the smart home more secure as the industry matures. Potential vulnerabilities identified in the report depend primarily on two scenarios – the installation of a malicious SmartApp or the failure of third-party developers to follow SmartThings’ guidelines on how to keep their code secure.
Regarding the malicious SmartApps described, this has not and will not affect our customers due to the certification and code review processes SmartThings has in place to ensure that malicious SmartApps are not approved for publication. To further improve our SmartApp approval processes and ensure that the potential vulnerabilities described continue to not affect our customers, we have added additional security review requirements for the publication of any SmartApp.
As an open platform with a growing and active developer community, SmartThings provides detailed guidelines on how to keep all code secure and determine which source is trustworthy. If the code is downloaded from an untrusted source, this can present a potential risk as when a PC user installs software from an unknown third party website, there is a risk that the software may contain malicious code. Following this report, we have updated our documented best practices to provide the best security guidelines for developers.


FTC: We use auto affiliate links to earn income. More.